An assault on the software program provide chain could be in course of, shaking the cryptocurrency ecosystem by means of JavaScript. In line with a bunch of laptop vulnerabilities researchers who write below the title of JDSTAERK, numerous NPM growth packages (nodes packages) acquired malicious updates.
Researchers would have found that the account of a developer referred to as “Qix” was violated, permitting The malicious code distribution in instruments that accumulate greater than 47 million downloads Weekly. Though it falls primarily on JavaScript builders all through the Web, the assault may not directly have an effect on finish customers to compromising cryptocurrency wallets.
The incident would have originated within the NPM repository, a platform that homes open supply packages important for the event of JavaScript purposes.
These packages, utilized by hundreds of initiatives worldwide, are widespread dependencies on servers and net purposes. The dedicated account would have allowed attackers Publish altered variations of fashionable packagesintroducing a malicious code designed to steal stealthily when stealing cryptocurrency funds.
In line with the evaluation printed within the jdstaerk.substack.com weblog, the malware is particularly activated when it detects the presence of a cryptocurrency pockets as Metamask.
The malicious code operates in two phases. If you don’t discover a purse, run a passive assault, attempting to ship information to an exterior server. Nonetheless, the true hazard arises when it detects an lively Pockets. On this state of affairs, malware intercepts communications between the pockets and the person, manipulating actual -time transactions from the clipboard of the working system.
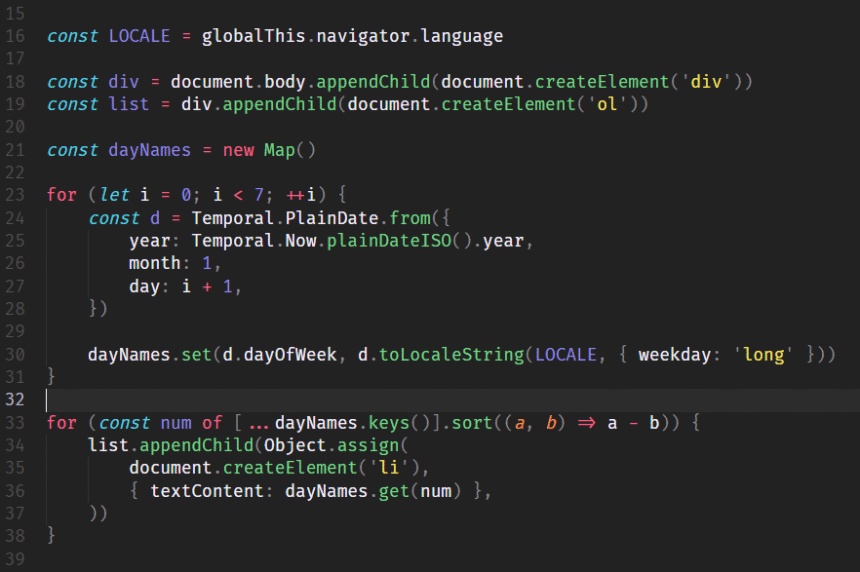
Researchers describe in additional element the fraudulent course of:
When the person begins a transaction (for instance, eth_sendTransaction), Malware intercepts the info earlier than sending them to the Pockets for its signature. Then modify the transaction within the reminiscence, changing the route of the respectable recipient with the route of an attacker. The manipulated transaction is forwarded to the person’s purse for approval. If the person doesn’t meticulously confirm the handle on the affirmation display screen, he’ll signal a transaction that sends their funds on to the attacker.
JDstaerk, group of investigators.
Though finish customers will not be the direct goal, the omnipresence of those packages in software program initiatives amplifies the chance, which isn’t straight talked about within the JDSTAERK evaluation.
Charles Guillemet, Cto de Ledger and who echoed the information, warns that Solely customers who use pockets {hardware} and may execute a visual and protected signature course of are protected in entrance of the software program provide chain assault.
(tagstotranslate) cyber assault