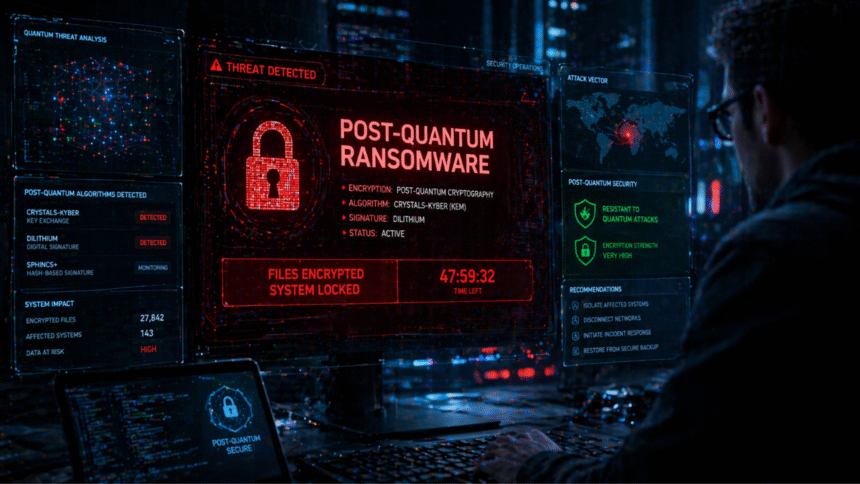
Cybersecurity agency Rapid7 revealed an evaluation that confirms, by way of reverse engineering, {that a} ransomware household referred to as Kyber makes use of ML-KEM 1024, a post-quantum cryptography commonplace authorised by the USA Nationwide Institute of Requirements and Expertise (NIST).
The aim of post-quantum shielding is shield the important thing with which you encrypt your victims’ recordsdatain line with the researchers within the report revealed this April 21 on the specialised website Ars Technica.
In line with Brett Callow, a menace analyst on the agency Emsisoft cited within the report, It’s the first confirmed case of a ransomware that makes use of post-quantum cryptography.
The Kyber household, energetic since at the very least September of final 12 months, takes its title from the ML-KEM commonplace itselfwhich is often known as Kyber in cryptographic literature.
The coincidence just isn’t coincidental, because the group behind the ransomware selected the title to focus on its use of the post-quantum scheme, whereas Rapid7 confirmed its implementation at the very least within the malware variant that assaults Home windows techniques.
Ransomware, however, is a sort of malicious software program that encrypts the sufferer’s recordsdata and calls for a cost, often in crypto property, in change for returning entry.
How does the post-quantum scheme work in Kyber?
In line with the evaluation, the malware doesn’t encrypt recordsdata instantly with the post-quantum commonplace, as this process could be too sluggish. As an alternative, it generates a random key beneath the AES-256 scheme (a symmetric encryption that’s already proof against quantum assaults) and encrypts the recordsdata with that key.
Then, use ML-KEM 1024 to guard AES key. That method, solely the attacker can recuperate the unique key and decrypt the info. In line with Anna Širokova, Rapid7 researcher and creator of the evaluation, implementing ML-KEM required little work: there are open supply libraries obtainable and properly documented that permit the scheme to be built-in by including a dependency to the undertaking.
Nevertheless, Rapid7’s analysis discovered that not all ransomware variants are per their very own claims.
The model of Kyber that assaults VMware techniques (a virtualization platform extensively utilized in company environments) claims to make use of ML-KEM, however reverse engineering revealed that it truly encrypts the important thing with 4,096-bit RSA. That conventional scheme would take even longer to be compromised by a quantum pc than ML-KEM itself.
Why do they use post-quantum safety in Kyber?
Probably the most hanging aspect of the evaluation is that Utilizing post-quantum cryptography brings no actual technical profit to attackers.
From Ars Technica they level out that quantum computer systems able to executing Shor’s algorithm (the mathematical process that may permit breaking the RSA and elliptic curve schemes) are at the very least three years away, and possibly far more. The Kyber ransom observe, however, offers victims only a week to pay. That point horizon makes any post-quantum benefit irrelevant.
In line with Širokova, the reply to why they use cryptography at Kyber is “victim-directed advertising”«. “Submit-quantum encryption sounds a lot scarier than ‘we use AES’, particularly for non-technical determination makers who’re evaluating whether or not to pay or not,” the researcher stated in an e mail cited by Ars Technica.
«It is a psychological trick. They are not frightened about somebody breaking encryption a decade from now. “They need cost in 72 hours,” he added. The goal just isn’t the technical groups of the sufferer corporations however the executives and attorneys who resolve whether or not to offer in to the rescue, and who They may affiliate the time period post-quantum with an insurmountable cryptographic energy.
The Kyber case is critical not a lot for its technical sophistication however for what it reveals in regards to the cyber menace ecosystem. Submit-quantum cryptography, a subject that till not too long ago circulated primarily in papers lecturers and analysis groups, is already recognizable sufficient to perform as a weapon of social engineering.